Essential Insights
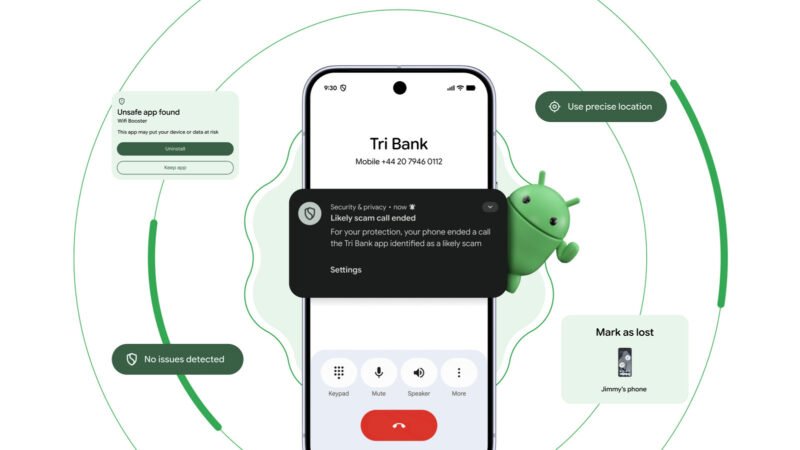
- Google introduces enhanced protections against banking scam calls on Android.
- Scam call protection automatically ends calls from impersonating bank numbers.
- Live Threat Detection expands to identify more suspicious app behaviors.
- New privacy tool allows temporary sharing of precise location data with apps.
### A Necessary Shield Against Evolving Scams
As cyber threats multiply, Google steps up its game. Recent announcements from the Android Show: I/O Edition reveal new security features aimed at keeping users safe from increasingly sophisticated scams. The focus on protecting users from banking scam calls illustrates both a timely response to a growing threat and a reminder of our vulnerability in this digital age.
Scammers have refined their tactics. They can now spoof calls, making it seem like they originate from legitimate banks. With the help of select financial institutions, Google introduces a spoofing protection feature. This tool will automatically end calls from numbers impersonating these banks and notify users about the potential scam. However, currently, this feature only works with banks not based in the U.S. Users in America will have to wait as Google expands partnerships with local banks. The effectiveness of these new tools hinges on timely adoption and broadening partnerships to ensure comprehensive coverage.
### Strengthening the Digital Fortress
Google’s commitment extends beyond just call protection. The company announced enhancements to its Live Threat Detection feature. This tool monitors app behavior, seeking out signs of deception or abuse. It will soon identify apps that forward SMS messages without consent or manipulate accessibility permissions. Users must trust that Google can recognize these threats before they become serious issues.
Device theft remains another significant concern. Google is implementing more robust settings for Failed Authentication Lock and allowing biometric locking. Once a phone is marked as lost, it will require biometric authentication for access. Users will gain peace of mind knowing that even a stolen device becomes largely useless without their biometric information.
A thoughtful approach to privacy accompanies these security measures. The option to share a precise location temporarily empowers users. This functionality helps users avoid giving permanent access to apps that don’t require it. Users can share location data only for specific tasks, thus maintaining control over their information.
Google’s enhancements represent a significant leap in protecting user data and security. As cyber threats evolve, so too must our defenses. These tools aim to create a more secure ecosystem for Android users, despite initial limitations in partnerships. By focusing on practical applications and user empowerment, Google takes meaningful steps to safeguard its community.
Stay Ahead with the Latest Tech Trends
Dive deeper into the world of Cryptocurrency and its impact on global finance.
Discover archived knowledge and digital history on the Internet Archive.
TechV1